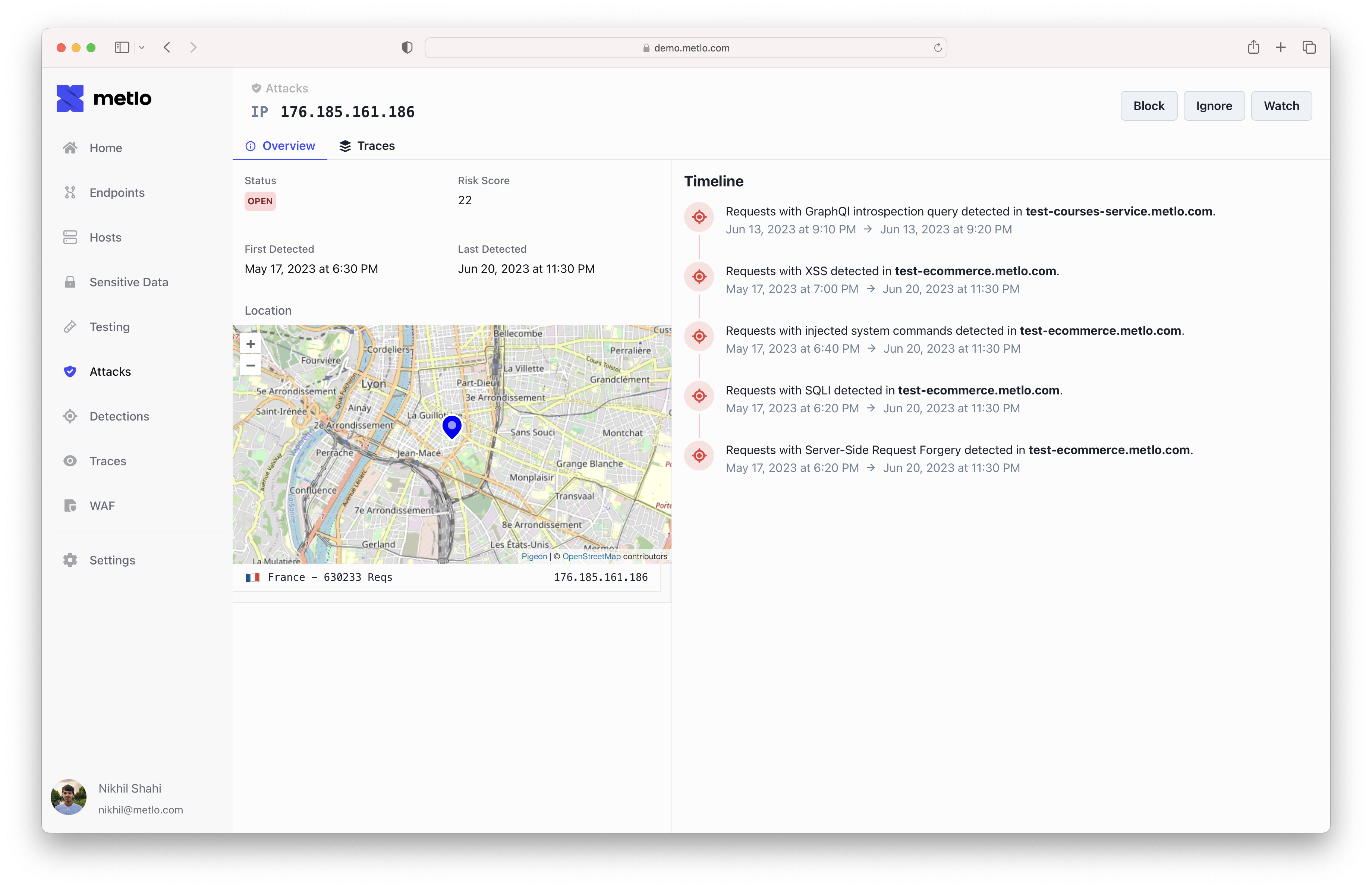
- SQL Injection
- Cross-Site Scripting
- Server-Side Request Forgery
- Remote Command Execution
- Directory Traversal
- GraphQL Introspection
- High rates of 401 errors
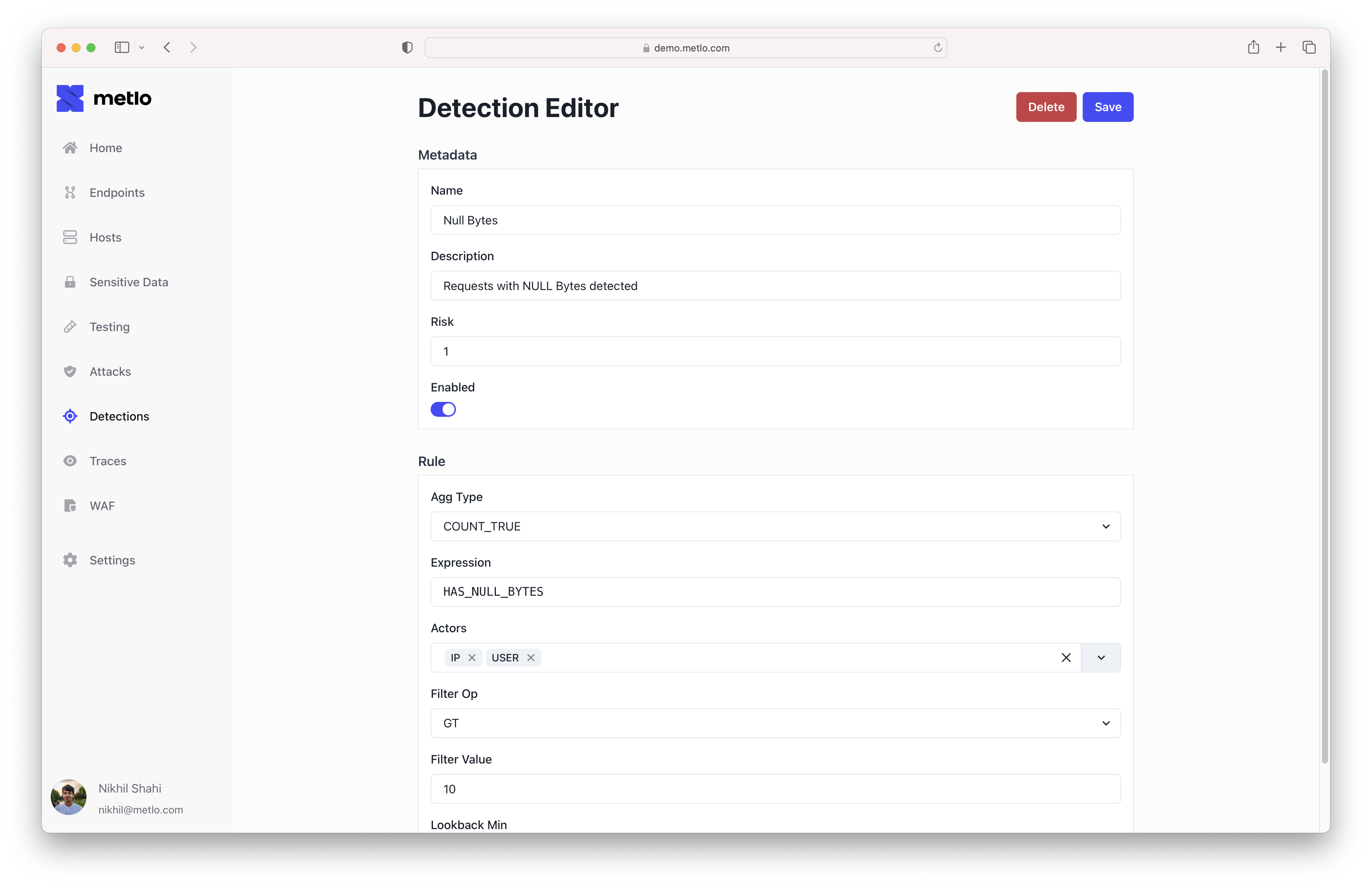
Detections
You can also build your own detections to customize how and what Metlo flags as an attack.